(Very) Basic Intro to Lattices in Cryptography
Lattice-based cryptography, an important contender in the race for quantum-safe encryption, describes constructions of cryptographic primitives that involve mathematical lattices. Lattices, as they relate to crypto, have been coming into the spotlight recently. In January 2019, Many of the semifinalists in the NIST post-quantum-cryptography competition were based on lattices. Lattice-based cryptography has promising aspects that give us hope for cryptographic security in a post-quantum world.
What is a Lattice?
According to Wikipedia, a lattice is the set of all integer linear combinations of basis vectors:
b1,...,bn E R^n
i.e.
L = { ∑ ai * bi : ai E Z }
More simply put, a lattice is defined by basis vectors, which are only able to be scaled by integers… yay no fractions!
For example, let’s create a lattice of all the integers in a two-dimensional plane:
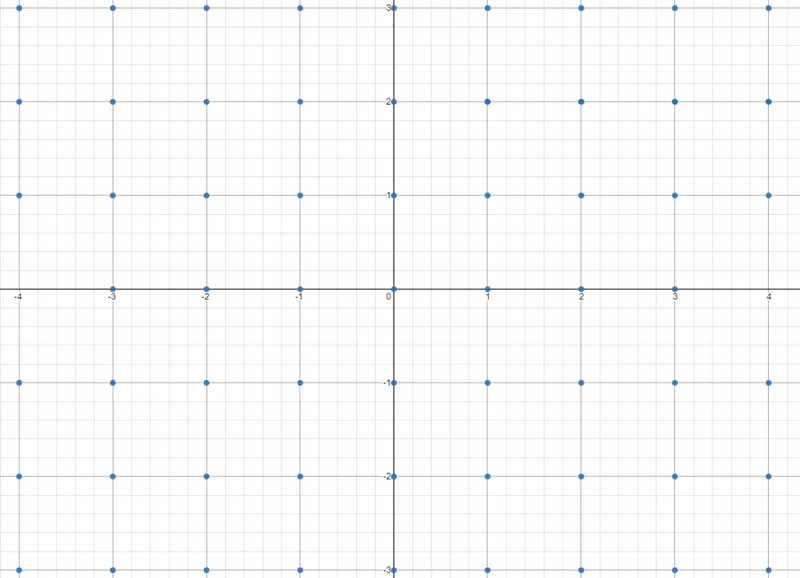
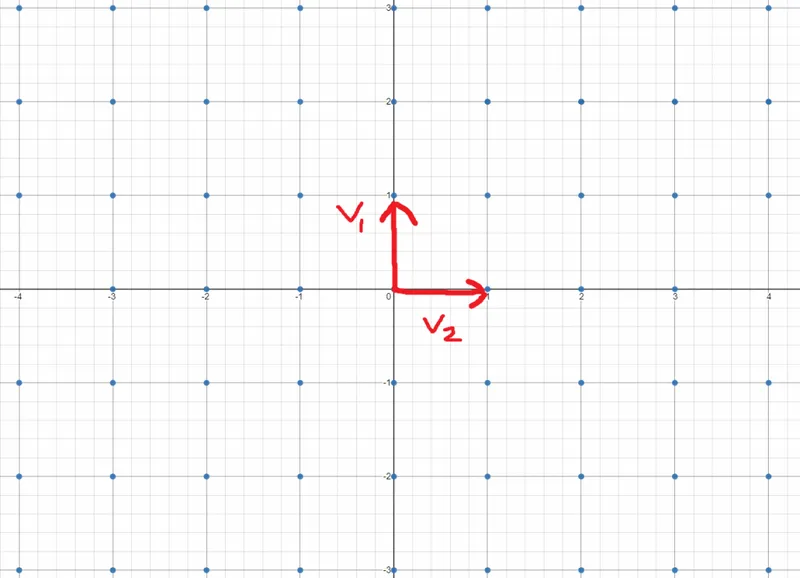
The definition of our lattice contains only 2 basis vectors,
v1 = (0,1)
v2 = (1,0)
Our lattice is the set of all values that can be reached by any combination and scale of our basis vectors. For example, the point (2,0) is in our lattice because it can be reached by 2*v1
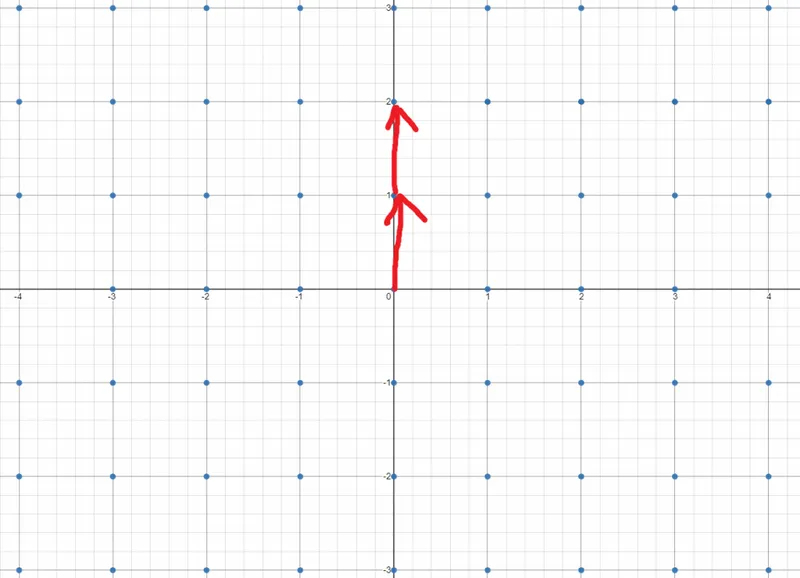
Similarly, we could create an entirely new lattice by changing our basis vectors to
v1 = (0,3)
v2 = (3,0)
As you can see, now the intermediary points (0,1) and (0,1) no longer exist in our lattice. There is no way to scale v1 (0,3) and v2 (3,0) to reach those points without using fractional scalars. With lattices, we can only scale by whole integers.
How Does This Help With Crypto?
Cryptographic algorithms are typically based on mathematical problems that are easy to verify the answer of, but hard to calculate.
For example, RSA is based on prime factorization. If I told you to find prime factors of 27,919,645,564,169,759, that would be hard. However, if I told you that 48,554,491 and 575,016,749 are prime factors, all you have to do is multiply them together to verify my answer.
RSA works great with classical computers. There are no known solutions to find prime factors of a number reliably in less than exponential time.
In the quantum world, things don’t look so peachy. Shor’s algorithm on quantum computers can crack RSA in less than exponential time. For this reason, we need quantum-safe algorithms. Many believe that lattice math could be an answer.
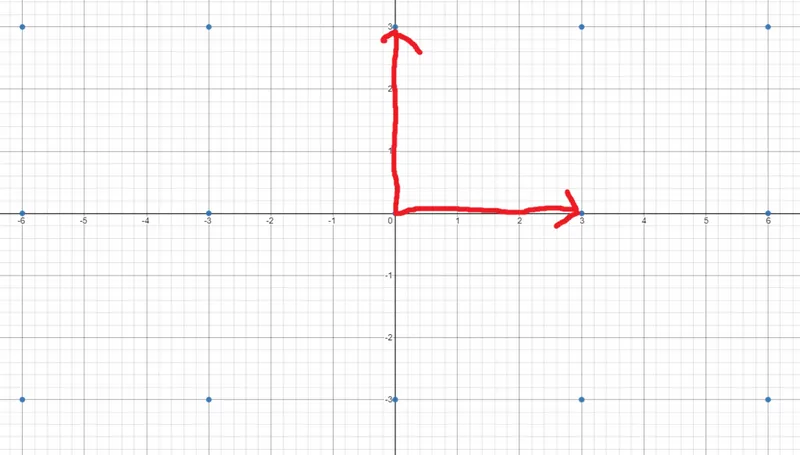
Shortest Vector Problem
The shortest vector problem (SVP) is one of the fundamentals problems presented by lattices that allow them to be useful in cryptography.
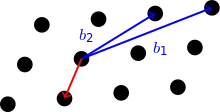
Simply put, the goal of SVP is for the attacker to find the shortest vector from the origin (above in red) when given the basis of a lattice (above in blue). A zero vector doesn’t work as an answer, we consider it trivial.
How is it solved?
Like RSA with classical computers, it is hard to find the shortest vector of a large lattice, especially if it exists in many dimensions. One such slow solution for approximating the shortest vector is Babai’s algorithm, or Nearest Plane Algorithm, which you can read about in the links provided.
Related Articles
What is SHA-256?
Jul 08, 2020 by Lane Wagner - Boot.dev co-founder and backend engineer
SHA-2 (Secure Hash Algorithm 2), of which SHA-256 is a part, is one of the most popular hash algorithms around. A cryptographic hash, also often referred to as a “digest”, “fingerprint” or “signature”, is an almost perfectly unique string of characters that is generated from a separate piece of input text. SHA-256 generates a 256-bit (32-byte) signature.
Why is Exclusive Or (XOR) Important in Cryptography?
Jan 18, 2020 by Lane Wagner - Boot.dev co-founder and backend engineer
If you are getting into cryptography, or just trying to understand the fundamentals, you may have noticed that the exclusive or (XOR) operation is used quite often, especially in ciphers. XOR is a simple bitwise operation that allows cryptographers to create strong encryption systems, and consequently is a fundamental building block of practically all modern ciphers. Let’s dive into the details and see what makes XOR so important.
(Very) Basic Intro to Hash Functions (SHA-256, MD5, etc)
Jan 01, 2020 by Lane Wagner - Boot.dev co-founder and backend engineer
Hash functions are used to securely store passwords, find duplicate records, quickly store and retrieve data, among other useful computational tasks. As a practical example, all user passwords on boot.dev are hashed using Bcrypt to ensure that if an attacker were ever to gain access to our database our user’s passwords wouldn’t be compromised.
Cryptology vs Cryptography - Definitions and Differences
Dec 16, 2019 by Lane Wagner - Boot.dev co-founder and backend engineer
Many new developers are jumping right into writing code, usually for those fat paychecks, without learning much about the history of Computer Science. Alan Turing is recognized as the father of Computer Science, though many don’t know that his roots were in cryptology and mathematics. It was out of cryptology, cryptography, and mathematics that computer science was born.